Employee account takeover can result in substantial losses for enterprises. Senior executives, board members, and employees with privileged access are all at especially high risk of being targeted, and attackers may use creative methods to infiltrate their accounts. While corporate logins can be protected by enterprise security teams, executives’ personal accounts fall outside of corporate control. If an executive’s personal password is exposed in a data breach, their unprotected accounts may provide entry points for a motivated attacker to access corporate resources.
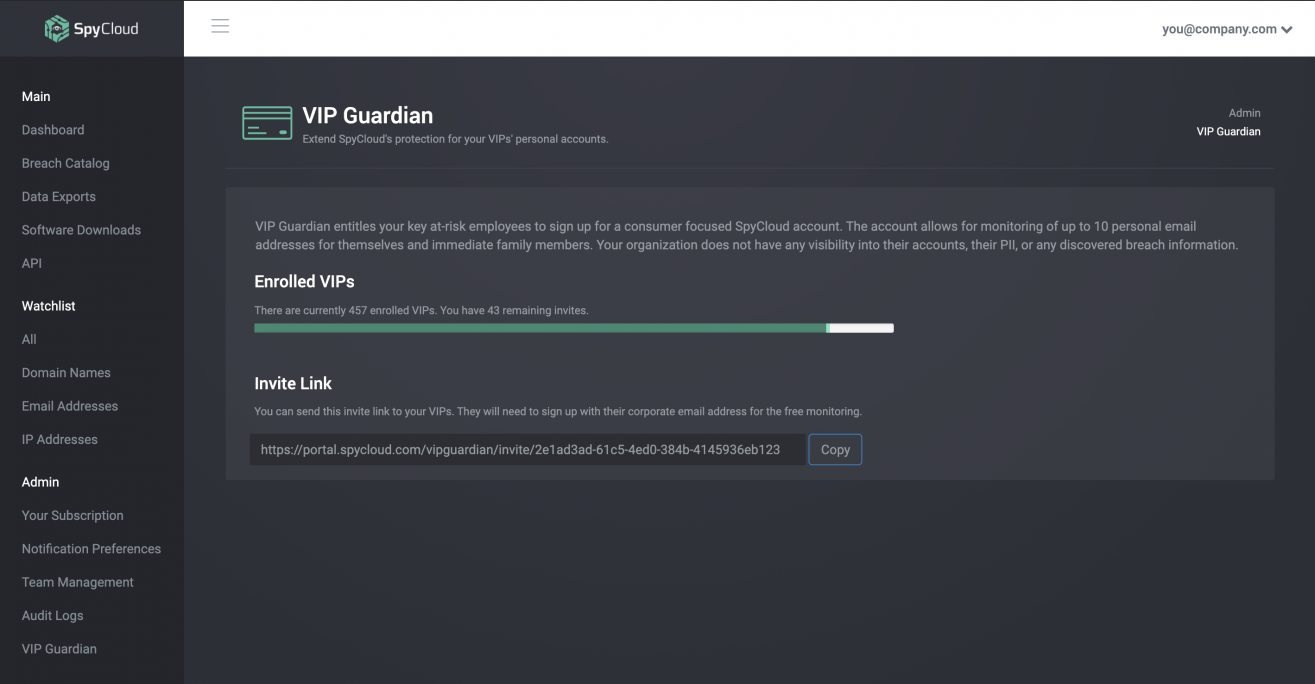
SpyCloud VIP Guardian helps you extend your employee account takeover prevention strategy to key executives’ personal accounts for an added layer of protection, without invading their privacy. With SpyCloud, you can give executives access to their own breach data and empower them to protect their vulnerable accounts.


Our CEO had his email account taken over and the cybercriminal sent out a bogus email to a finance associate claiming Buckman’s financial officer authorized a wire transfer.
CHEMICAL
Learn How Buckman Identified Over 2,000 Exposed Employee Accounts with SpyCloud

While your enterprise can monitor corporate credentials for breach exposures to keep attackers out of enterprise accounts, executives may reuse exposed passwords across personal logins that your security team can’t monitor, including online banking, tax preparation, health services, and any number of other accounts that an attacker could use or monetize. Any one of these accounts could provide a stepping stone to your enterprise resources, perhaps by enabling a threat actor to impersonate the executive and social engineer colleagues into taking risky actions. SpyCloud VIP Guardian enables you to reduce these security blindspots.
With SpyCloud VIP Guardian, your highest-risk executives can monitor their own personal and family accounts for stolen passwords that can put their finances, personal data, and identities at risk. The steps they take to secure their vulnerable personal accounts will also bolster your corporate security, in ways your security team wouldn’t be able to do alone.
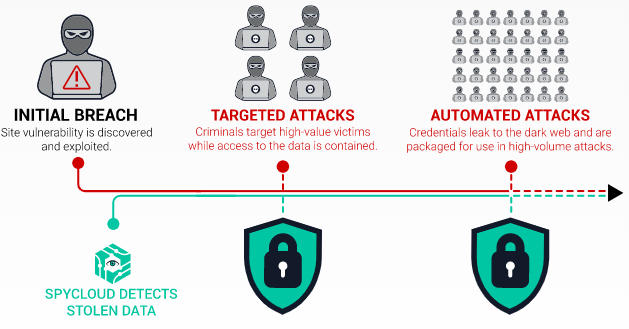
In the first 18 to 24 months after a breach occurs, attackers typically restrict access to stolen data to a select group of associates. This time allows them to squeeze out as much profit as possible before the data leaks to a broader audience. While the data is fresh, attackers are likely to use stolen credentials for targeted attacks against high-value victims, which may include your board members or executives.
SpyCloud uses human intelligence to recover stolen data as soon as possible after a breach occurs to help enterprises stay ahead of targeted attacks. With SpyCloud VIP Guardian, your executives will find out quickly if any of their personal information or passwords have been exposed in a new breach, giving them time to protect their vulnerable accounts.

If you get your password compromised in one place, you can bet it’s compromised everywhere you reuse passwords. We need users to understand the many dangers that are inherent with emails and passwords.
HIGHER EDUCATION
Learn How a Oklahoma University Detected 1,000 Exposed Users within 30 Minutes with SpyCloud
Helping key executives monitor their personal breach exposure can reduce the avenues a criminal has to access enterprise resources, but it’s just one piece of the puzzle. You should also monitor the corporate credentials of your entire employee base for compromised passwords that put your enterprise at risk.
SpyCloud Employee ATO Prevention enables security teams to check and reset exposed employee passwords as soon as possible after a breach to lock out cybercriminals.
